Security Controls that prevents data loss and control the data flow throughout the entire life cycle: data in rest, in motion and in use.
Encryption / Key Management Systems
Encryption key management is administering the full lifecycle of cryptographic keys and protecting them from loss or misuse.
The lifecycle includes: generating, using, storing, archiving, and deleting of keys. Protection of the encryption keys includes limiting access to the keys physically, logically, and through user/role access.
Data classification
Regain control over your unstructured data.
By classifying your data you can retrieve it more easily and identify more accurately the data you need to protect.
Data classification can reduce the risk of costly data leakage and increase the efficiency of your business. Using classification to automatically apply data protection measures, your data security doesn’t have to be left to chance.
File integrity monitoring (FIM)
FIM is a control that involves examining files to see if and when they change, how they change, who changed them, and what can be done to restore those files if those modifications are unauthorized.
FIM is useful for detecting malware as well as achieving compliance with regulations like the Payment Card Industry Data Security Standard (PCI DSS).
Secure Information Sharing
If access to the systems holding your sensitive information can’t be managed, you have a significant governance issue.
Sharing information inappropriately or carelessly can pose a significant risk to your organisation, leaving it vulnerable to theft, loss of data or improper use of information. Understanding how to manage information in a way that keeps it protected and secure is crucial.
Ensure that staff, contractors, suppliers and other organisations that handle (send, receive or store) your information are clear on their responsibilities to protect it securely.
Issues to address:
- Are your policies on information sharing clearly and effectively communicated with staff, contractors, suppliers and others with access to your information?
- Does your policy cover all mechanisms for sharing information: email, removable hardware (disks or memory sticks), post, hard copy, mobile devices and in person?
- Is there clarity on which information or data is critical to your organisation?
- How is confidential information or data managed or stored? Is there clarity on how this information is handled and managed?
Information Governance / Data Analytics
Information Governance can facilitate the effective and efficient use of information in any organization, helping them to achieve their goals.
You can control the acquisition, management, retention and disposal of all enterprise information – both structured and unstructured – within your business to help reduce risk, ensure compliance and increase business productivity and efficiency.
Use Data Analytics technologies to examine data sets in order to draw conclusions about the information they contain and be able to make more-informed business decisions.
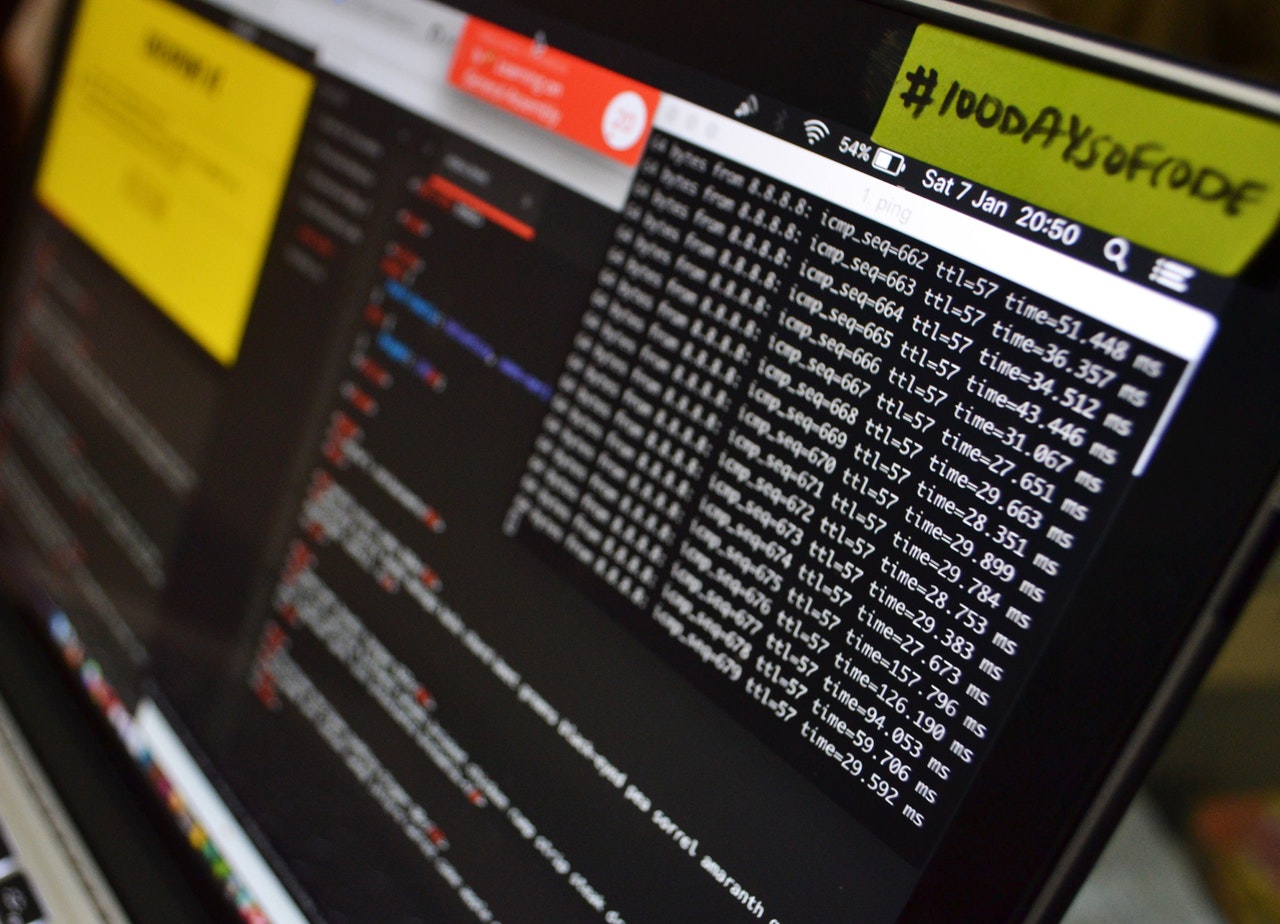
Data Loss Prevention
Are technologies that, as a core function, perform both content inspection and contextual analysis of data at rest on-premises or in cloud applications and cloud storage, in motion over the network, or in use on a managed endpoint device.
The solutions incorporate sophisticated detection techniques to help organizations address their most critical data protection requirements.
Leading characteristics of enterprise DLP solutions include a centralized management console, support for the advanced policy definition and event management workflow. Enterprise DLP functions as a comprehensive solution to discover sensitive data within an organization and mitigate the risk of its loss at the endpoints, in storage and over the network.
Data discovery / management
Data discovery is the process of collecting data from your various databases and silos, and consolidating it into a single source that can be easily and instantly evaluated.
Data security / Secure Mail
Provides email encryption capabilities for enterprises.
5 key benefits of having encrypted email:
- Protects private information – A lot of private information and trade secrets are exchanged over email, which is why it is imperative to make sure that only the intended recipients see the information. It’s important that hackers are unable to decrypt the information that is being passed between individuals.
- Cost-effective – When the email service already has encryption integrated into the server, there is no need to purchase additional equipment. Many companies have purchased their own servers when it may not be necessary. That’s a lot of money that could have been saved. A trusted third-party service costs much less.
- Timesaving – When email is already encrypted, there’s no need to take additional steps to ensure security. In the past, people would have to use multiple programs to secure their connection so that the information they were about to share would be private. There is no longer a need for this with the right technology. The email provider handles all the legwork.
- Regulation compliance – Different industries have certain regulations that must be followed when it comes to communication. HIPAA, for instance, requires patient information to be confidential. Information is to not be shared without the consent of the patient. A hacker getting hold of patient information is a violation.
- Avoids spam – Spam attachments tend to contain viruses. Hackers get in in this way. When you or someone else sends attachments using encrypted email, the email contains a digital signature that shows it is genuine. That way, no one is opening spoofed emails.