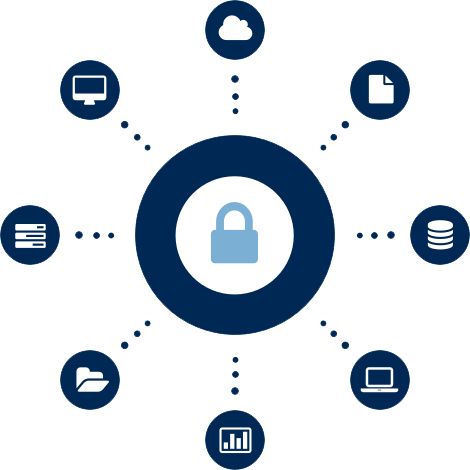
Security Controls that protects the database.
Database Encryption
Is used to protect data within relational database management systems (RDBMSs). Encryption can be implemented using native DBMS tools, third-party software tools and network-based appliances, or implemented within storage networks via fabric-based encryption. Clients that enable built-in encryption are increasingly implementing database encryption as a regulatory check box.
The organizations have the flexibility to encrypt data at multiple levels and during multiple processes.
The solutions deliver powerful protection for the sensitive corporate and customer information stored in databases.

User Benefits:
-
- Granular protection—Retain ownership of data throughout its life cycle with granular file- or column-level encryption.
-
- Centralized administration—Simplify security administration and control costs with centralized management of keys, policies, and configurations.
-
- Controlled access—Ensure regulatory compliance and reduce risks by setting policies for separation of administrative duties.
-
- Productivity empowered—Encrypt information transparently, without disrupting business operations, database performance, or the end-user experience

Database Activity monitoring (DAM)
It’s tracking and auditing what someone did with their access/account.
It refers to a suite of tools that can be used to support the ability to identify and report on fraudulent, illegal or other undesirable behavior, with minimal impact on user operations and productivity.
The tools, which have evolved from basic analysis of user activity in and around relational database management systems (RDBMSs) to encompass a more comprehensive set of capabilities, such as discovery and classification, vulnerability management, application-level analysis, intrusion prevention, support for unstructured data security, identity and access management integration, and risk management support.
Database activity monitoring provides the robust compliance and security coverage necessary for protecting your data, without the costs associated with native database auditing.







