Privileged Access Management (PAM)
Consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for users, accounts, processes, and systems across an IT environment.
How PAM help organizations?
Condensing their organization’s attack surface and preventing, or at least mitigating, the damage arising from
external attacks as well as from insider malfeasance or negligence.
Through streamlining the authorization and control of privileged accounts,
PAM lets organizations stay in control and be safe from both intentional and unintentional admin rights abuse.
Privilege access management helps manage entitlements, not only of individual users but also shared accounts such as super users, administrative or service accounts. A PAM tool protects and manages all types of privileged accounts.
Mature PAM solutions go even further than simple password generation and access control to individual systems, and also provide a unified, robust, and—importantly—transparent platform integrated into an organization’s overall identity and access management (IAM) strategy.
Difference between the two major
categories of IT accounts
User Accounts
A user account typically represents a human identity (such as an Active Directory user account) and has an associated password to Protect information and prevent anyone else accessing without permission. There is usually a single account password per user that needs to be memorized by a person.
Privileged Accounts
Privileged accounts provide administrative or specialized levels of access to enterprise systems and sensitive data, based on higher levels of permissions. A privileged account can be associated with a human being or non-human IT system.
Organizations often have two to three times more privileged accounts than they have employees. In most organizations, IT staff have one account with standard-level permissions and another account for performing operations that require elevated permissions.

Privileged accounts are the keys to your IT, since they can be used to:
-
-
- access a sensitive server
- adjust permissions
- make backdoor accounts
- change or delete critical data
-
What are the risks associated
with unmanaged privileged accounts?
Many recent high-profile breaches have one thing in common: They were accomplished through the compromise of privileged credentials. Industry analysts estimate that up to 80% of all security breaches involve the compromise of privileged accounts.
Virtually all organizations have some unknown or unmanaged privileged accounts, increasing their risk. Some may have thousands. This can happen for various reasons:
-
-
-
- An ex-employee’s access was never disabled.
- An account is utilized less and less often until it becomes obsolete and is abandoned.
- Default accounts for new devices were never disabled.
-
-
How do cyber-criminals
compromise privileged accounts?
01. Compromise a local account.
Criminal hackers use malware or social engineering to get access to desktops, laptops, or servers. Employees are typically fooled by phishing scams that appear to be legitimate requests from an employee’s manager, company executive, or another trusted source. They may unknowingly click on a malicious link, download a piece of software with malware hidden inside, or enter their password credentials into fake websites.
02. Capture a privileged account.
An attacker’s primary goal is to obtain a privileged account (such as a local Windows administrator account) to move around. After an employee’s password is captured, the perpetrator can log onto a network and simply bypass many of the traditional IT security controls because they appear as a user with legitimate credentials. Common techniques include Man in the Middle or Pass the Hash attacks to elevate privileges.
03. Hide and observe.
Sophisticated criminal hackers are patient, preferring to remain undetected rather than crack-and-dash. After attackers establish a breach, they typically use compromised privileged accounts to perform reconnaissance and learn about the normal routines of IT teams. This includes observing regular schedules, security measures in place, and network traffic flow. They use these observations to blend in and make sure they don’t trigger any network security alarms. Eventually they can get an accurate picture of the entire network and its operations.
01. Compromise a local account.
Criminal hackers use malware or social engineering to get access to desktops, laptops, or servers. Employees are typically fooled by phishing scams that appear to be legitimate requests from an employee’s manager, company executive, or another trusted source. They may unknowingly click on a malicious link, download a piece of software with malware hidden inside, or enter their password credentials into fake websites.
02. Capture a privileged account.
An attacker’s primary goal is to obtain a privileged account (such as a local Windows administrator account) to move around. After an employee’s password is captured, the perpetrator can log onto a network and simply bypass many of the traditional IT security controls because they appear as a user with legitimate credentials. Common techniques include Man in the Middle or Pass the Hash attacks to elevate privileges.
03. Hide and observe.
Sophisticated criminal hackers are patient, preferring to remain undetected rather than crack-and-dash. After attackers establish a breach, they typically use compromised privileged accounts to perform reconnaissance and learn about the normal routines of IT teams. This includes observing regular schedules, security measures in place, and network traffic flow. They use these observations to blend in and make sure they don’t trigger any network security alarms. Eventually they can get an accurate picture of the entire network and its operations.
04. Impersonate employees.
An attacker with access to a privileged account can impersonate a trusted employee or system and therefore can carry out malicious activity without being detected as an intruder. When attackers compromise a privileged account, they can operate undetected for weeks or months at a time. Because a compromised privileged account appears to be a legitimate user, it’s very difficult to find the root cause or perform digital forensics when a breach is eventually detected.
05. Establish ongoing access.
An attacker’s next step is often to establish ongoing access by installing remote access tools, which enables them to return anytime they wish and perform malicious activities without raising an alarm.
06. Cause harm.
Depending on the motive of the attackers, they can use privileged accounts to do things such as:
- Damage system functions or disable access by an IT administrator
- Steal sensitive data for fraud or reputation damage
- Inject bad code
- Poison data
Why is PAM important?
A well-executed privileged access management strategy establishes regulated individual user access controls and behaviour transparency to mitigate security risks. PAM tools are introduced to ensure that users only have access to what is required to do their job and nothing more.
Why would I need PAM?
PAM keeps your organization safe from accidental or deliberate misuse of privileged access.
Some of these admin users can override existing security protocols.
PAM solves this problem.
A PAM solution offers a secure, streamlined way to authorize and monitor all privileged users for all relevant systems.
- Grant privileges to users only for systems on which they are authorized.
- Grant access only when it’s needed and revoke access when the need expires.
- Avoid the need for privileged users to have or need local/direct system passwords.
- Centrally and quickly manage access over a disparate set of heterogeneous systems.v
- Create an unalterable audit trail for any privileged operation.
Capabilities of the PAM solution
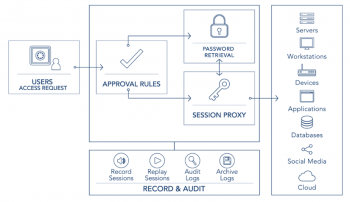
Components of a PAM Solution
Privileged Access Management solutions vary in their architectures, but most offer the following components working in concert: