Security Controls that manage user access, the ID’s, the data governance in order to prevent against insider threats, controls sensitive information and limit user errors.
Multifactor Authentication (MFA)
Security system that requires more than one method of authentication from independent categories of credentials to verify the user’s identity for a login or other transaction.
Multifactor authentication combines two or more independent credentials: what the user knows (password), what the user has (security token) and what the user is (biometric verification).
The goal of MFA is to create a layered defense and make it more difficult for an unauthorized person to access a target such as a physical location, computing device, network or database. If one factor is compromised or broken, the attacker still has at least one more barrier to breach before successfully breaking into the target.
User and Entity Behavior Analytics (UEBA)
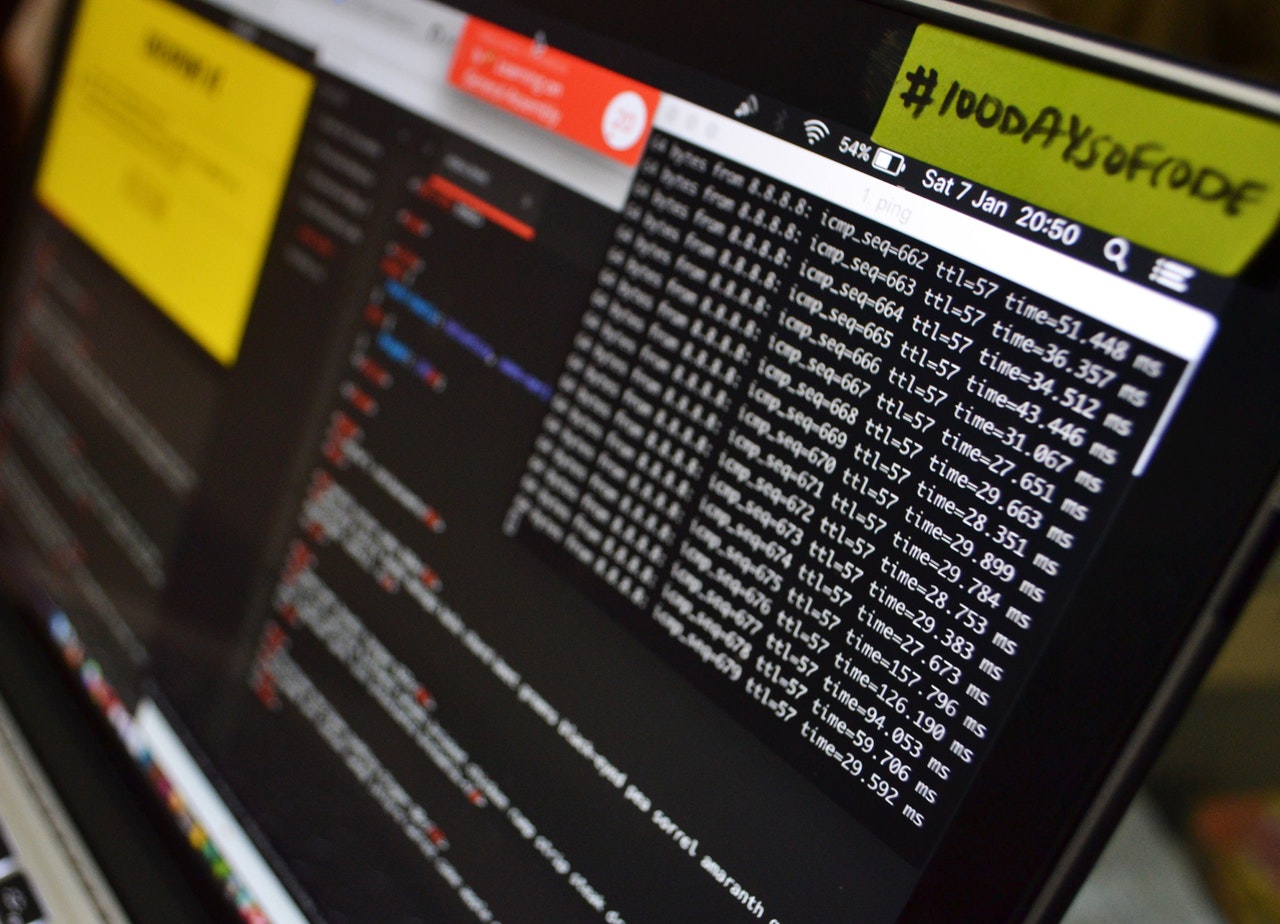
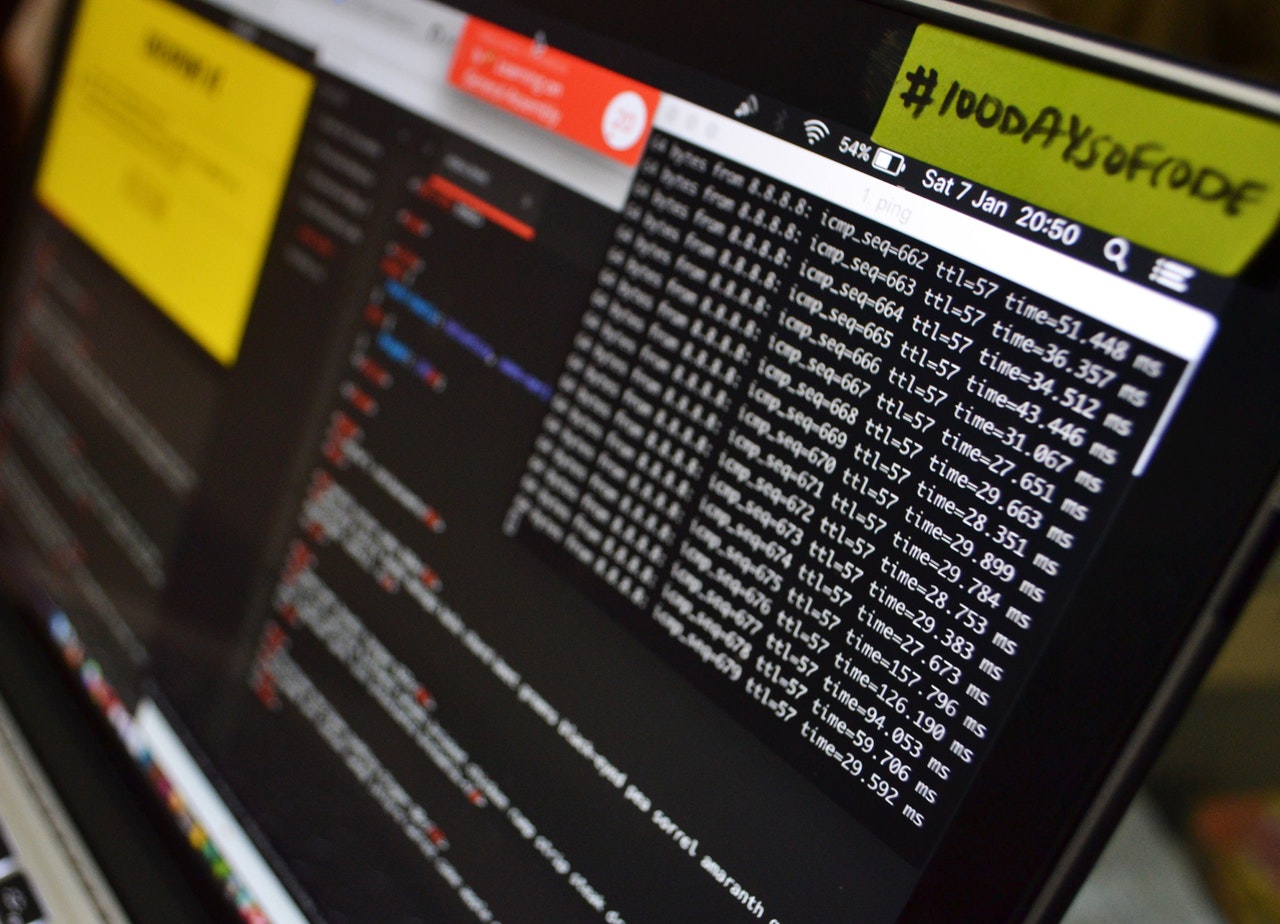
User behavior analytic tools are different in that they shift the focus from sending alerts of potential threats from outside the network to identifying more concentrated and individualized insider threats based on user behavior.
Is a type of machine learning model that can help to foil cyberattackers by discovering security anomalies.
UEBA uses advanced analysis; aggregates data from logs and reports, and looks at packet, flow, file and other types of information, as well as certain kinds of threat data to figure out whether certain kinds of activity and behavior are likely to constitute a cyberattack.
Benefits of User Entity Behavior Analytics (UEBA):
- Detection of hijacked accounts
- Reduced Attack Surface
- Privilege Abuse and Misuse (UEBA’s algorithms ensure that the access rights are used appropriately and give an overview of what kind of privileges individual users should have)
- Improved Operational Efficiency
- Data Exfiltration detection